Published June 2023
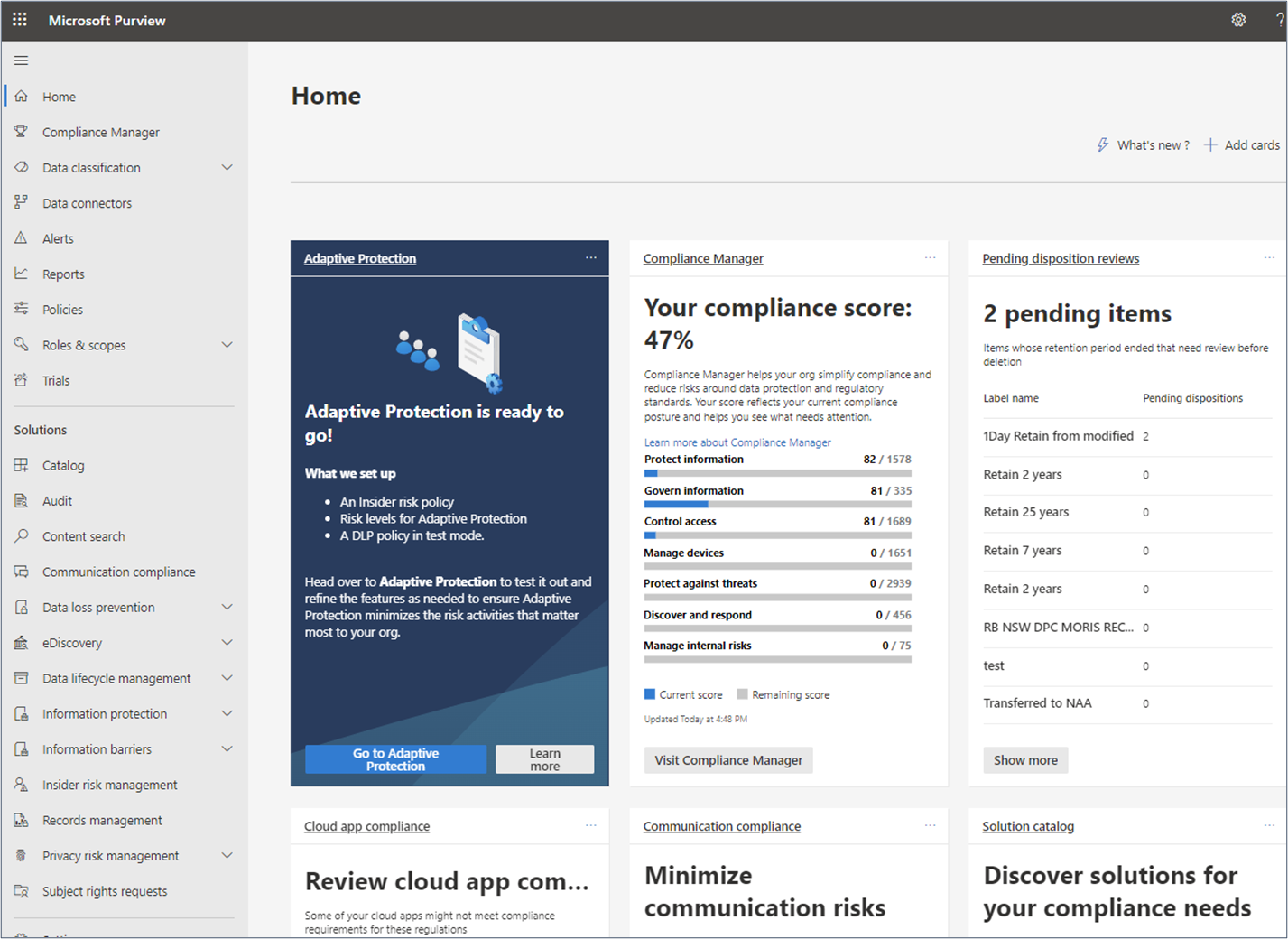
Keeping up to date with all the improvements from Microsoft in the Purview compliance portal can be a full-time job. Luckily for you, that’s our job and we’re here to cut through the noise and share insights on the right things to care about.
Microsoft are constantly improving and adding to the set of tools available in the Purview compliance portal (previously Microsoft 365 Compliance) to monitor and protect information in M365. In many of our client engagements, we find that information managers are often unaware of the full capabilities of Purview or even that they already have access to it thought their E3, E5 or equivalent licencing.
This blog will not attempt to describe all of the functionality available in Purview, instead it will give you an outline of the tools available and take a look at the Information Protection module in more detail. Enjoy!
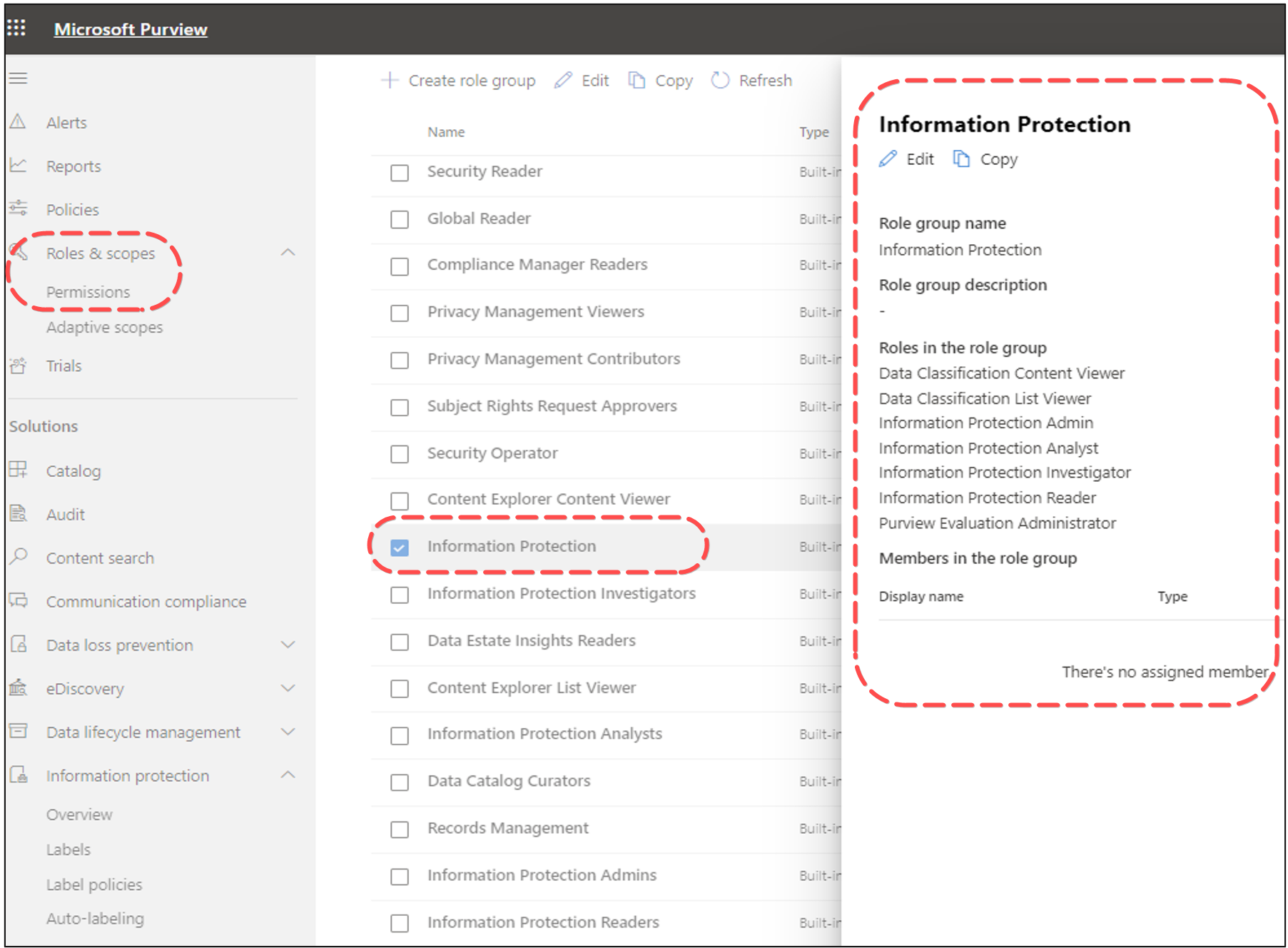
Permissions in Purview
The first thing to check is whether you have access to the relevant Purview modules. Purview has a comprehensive set of pre-defined role groups and roles and to be able to use the various components, you need to be either a global administrator or a member of one or the Purview role groups. Using the new Permissions page, you can manage permissions to users for various compliance tasks in features like Data Loss Prevention, eDiscovery, information protection management and retention. Users can only perform the compliance tasks that you explicitly grant them access to. In many organisations, access to this page is often restricted to IT administrators, so if you are unable to view it, you will need to speak to your IT department.
Once you have the required access you will be able to use a wide range of tools to discover, protect and monitor your information. To use the Information Protection module discussed below, you need to be assigned the Information Protection role group to use the full functionality or a more restricted group such as Information Protection Analyst or Information Protection Reader, depending on your role.
The screenshot below shows the roles that make up the ‘Information Protection’ role group.
Purview Components
Depending on your permission levels, you will see a range of available solutions. The ‘Solutions catalogue’ page provides a summary of the main components available to you.
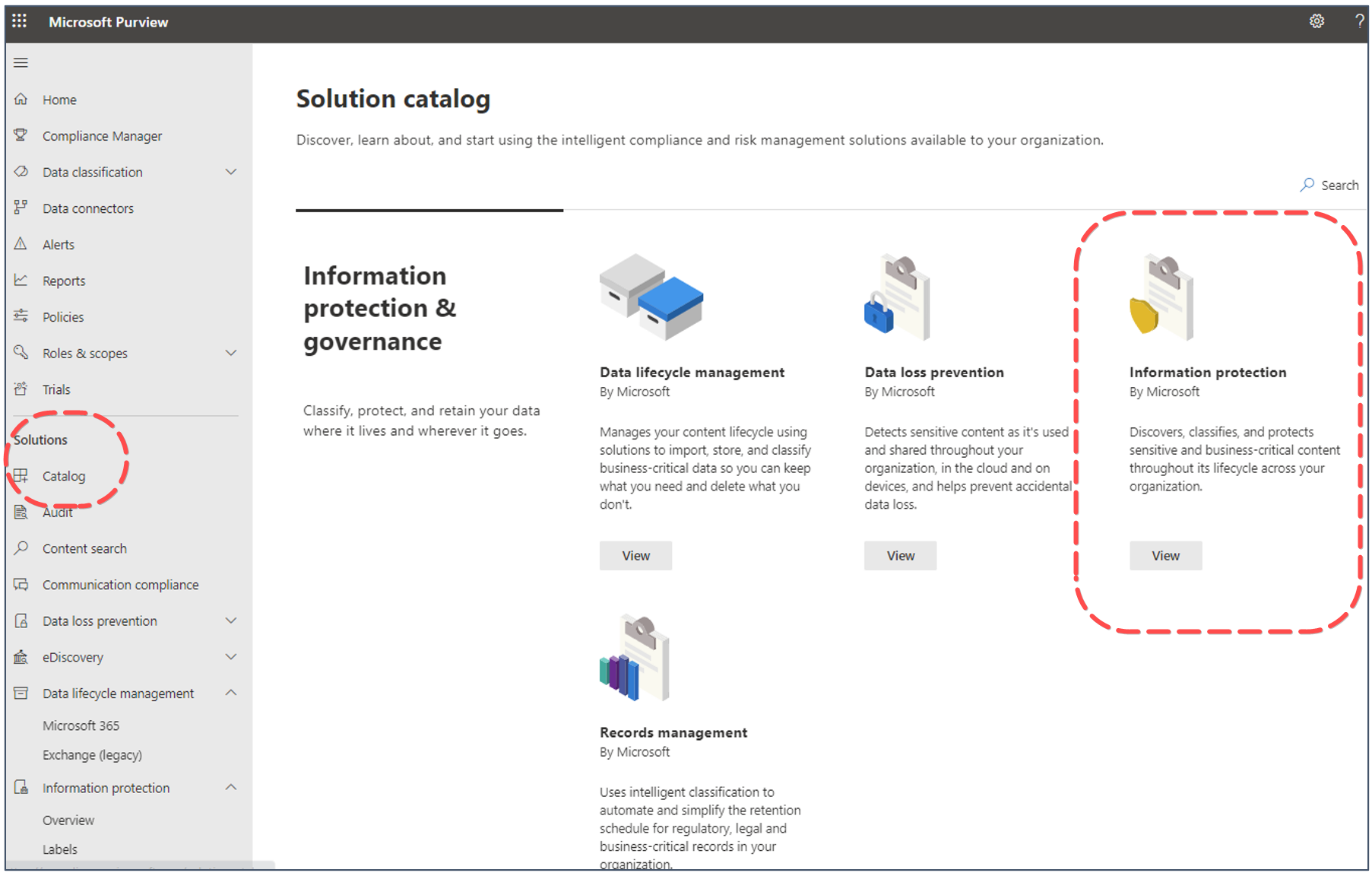
Purview Information Protection
Let’s take a look at the Information protection module in more detail…
This module allows you to discover, classify and protect sensitive content throughout its lifecycle. You do this by creating and publishing Sensitivity Labels. Sensitivity labels are used to classify email messages, documents, sites, and M365 groups. When a label is applied, either automatically or manually by a user, the content or site is protected based on the settings you have selected.
This can range from basic content marking, controlling access to a specific site or encrypting files. At a high level, the process involves:
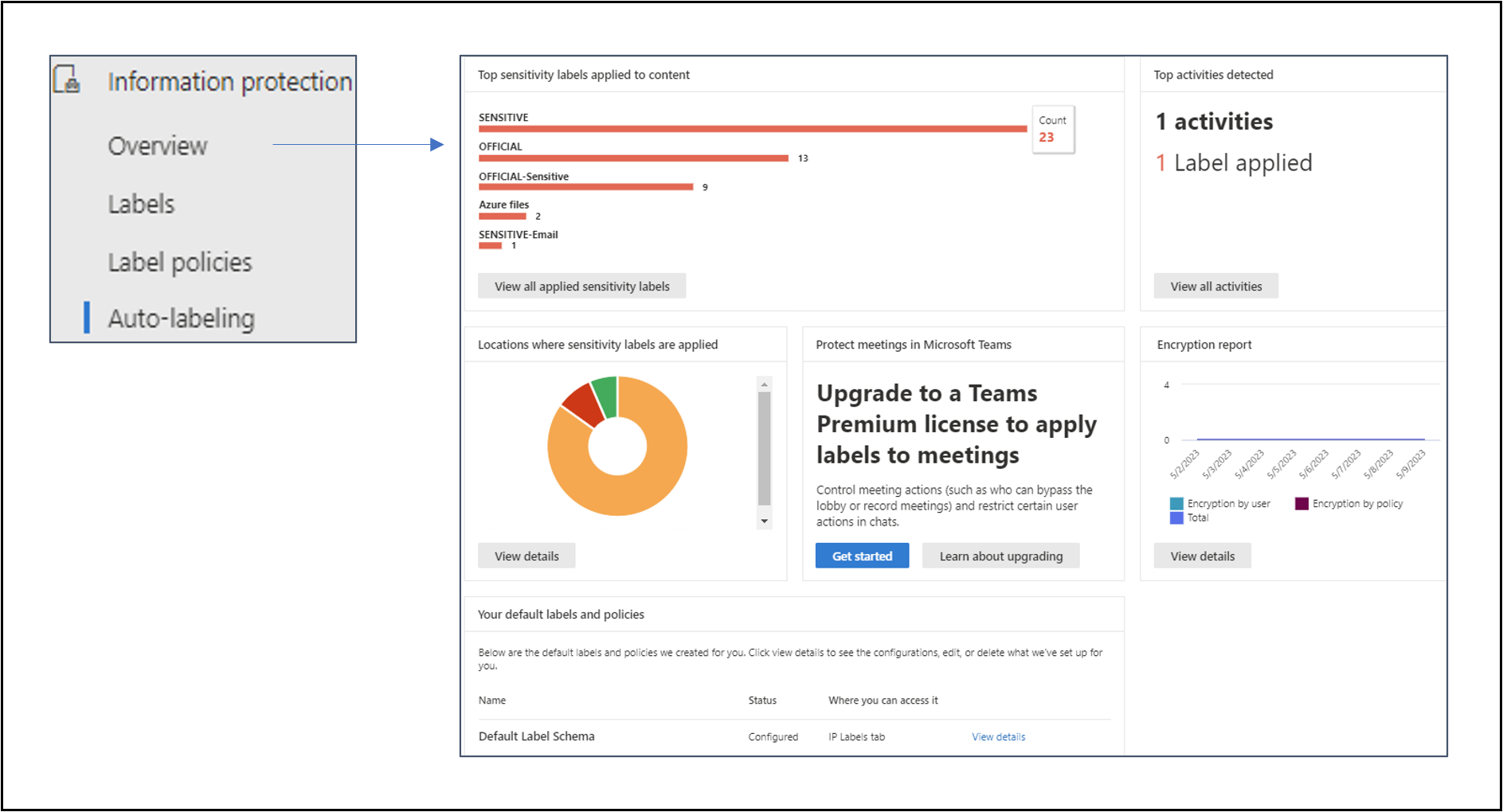
Information Protection Overview page
The ‘Overview’ window provides a visual summary of your sensitivity label activity. From here you can easily see which labels have been applied and in which locations.
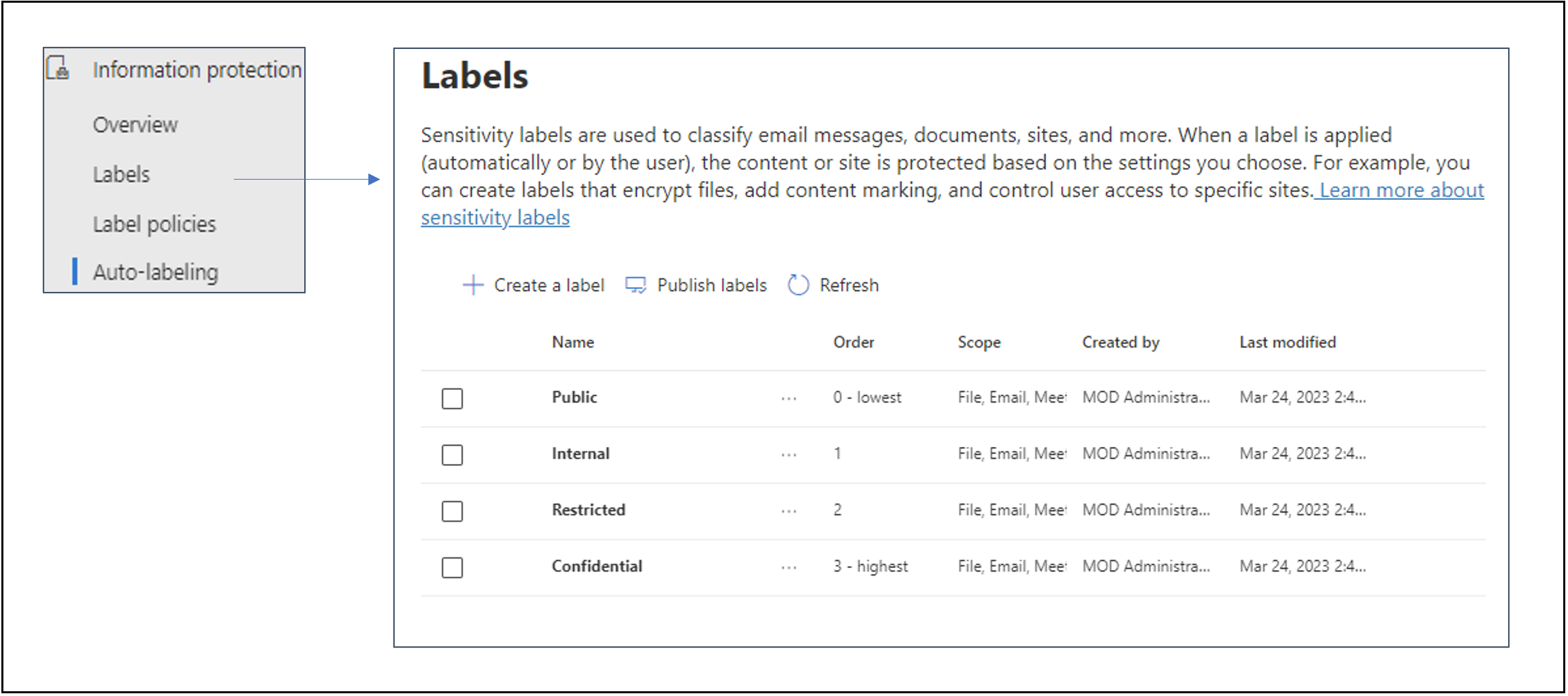
Labels
The ‘Labels’ page is where you will create your sensitivity labels. Once you have created a label you make it available by publishing it to users, distribution groups, mail-enabled security groups and M365 Groups.
There are a wide range of options available when defining a sensitivity label. The workflow diagram below summarises the steps and options.
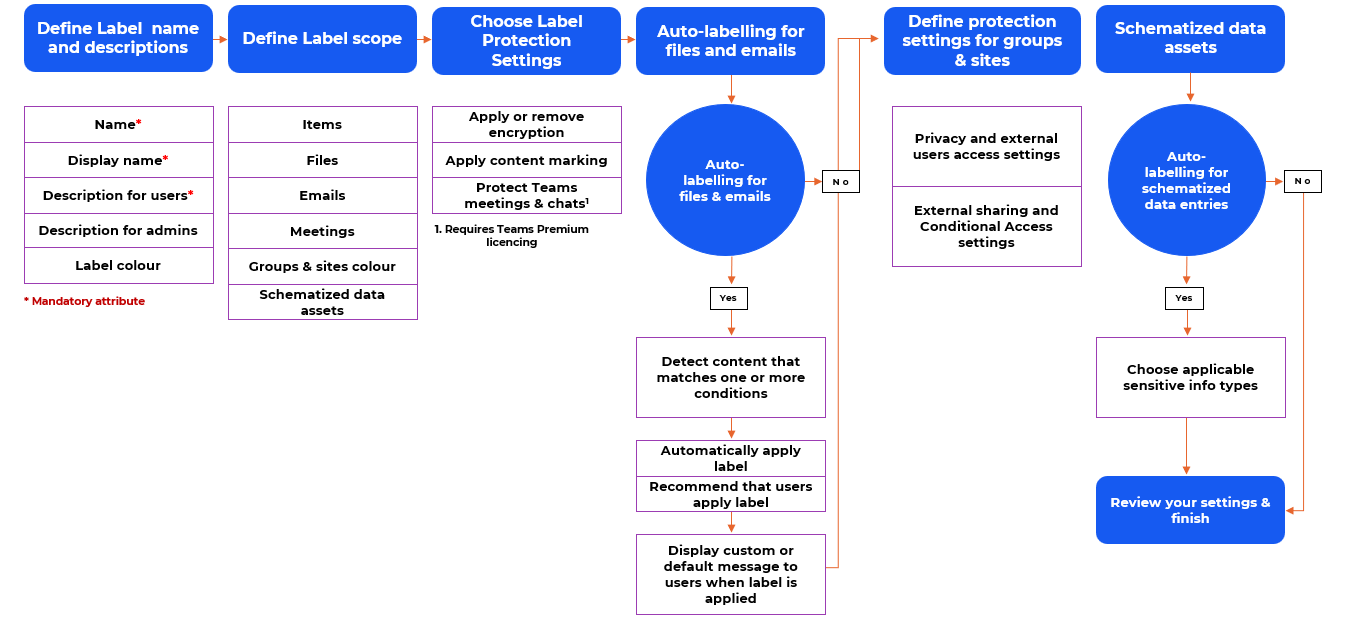
Sensitivity labels can range from fairly basic – simple content marking of documents and emails to more complex – a label that applies encryption to content and restricts access and sharing to a specific set of users. A good way to become familiar with the options is to start by creating one or two labels with simple scope and settings and publish them to a small number of users. Once you are comfortable with the basic options, create more complex labels until you understand the full spectrum of available functionality.
Label policies and Auto-labelling
Once you have created your labels, you need to make them available, either manually, through a label policy or automatically through an auto-labelling policy.
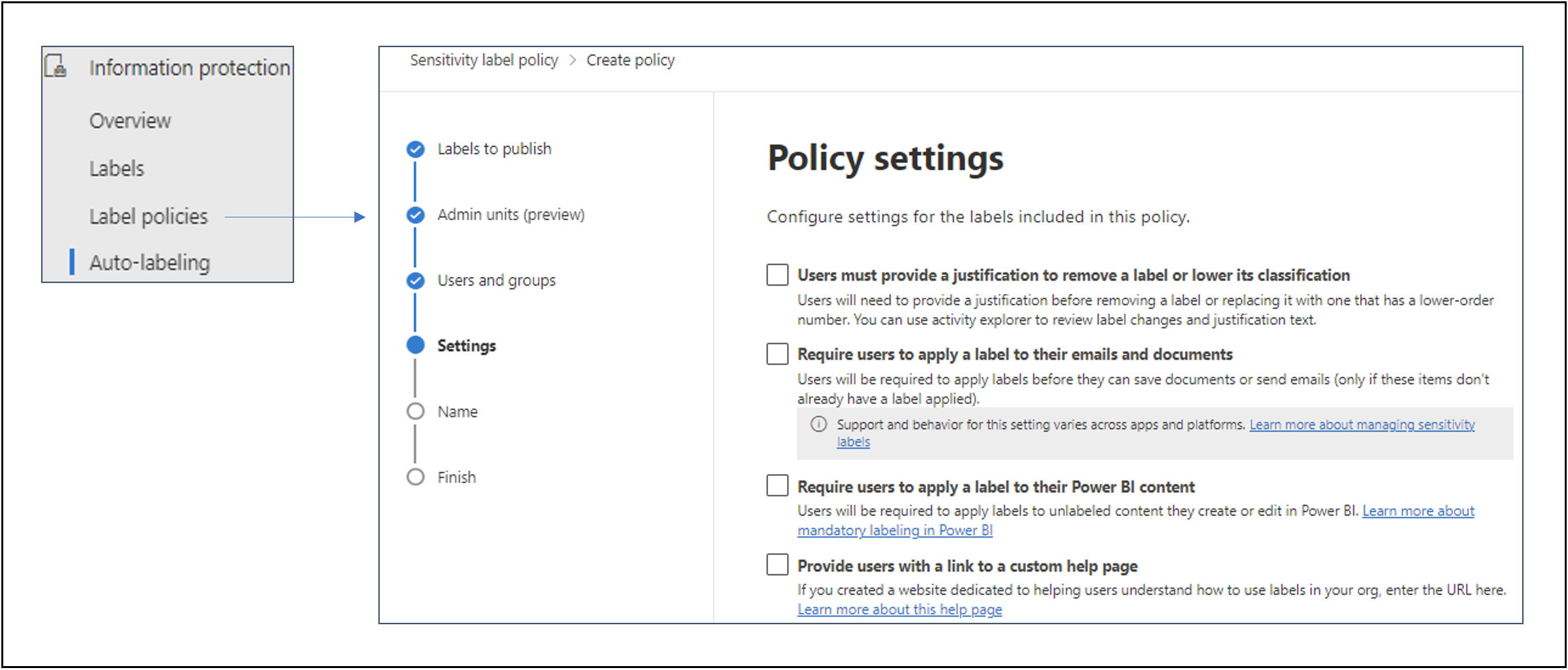
There are a number of configuration options available when you publish a label. Different settings can be applied to different labels, depending on your use case. Some of the common options include:
- Default labels – should a default label be set for documents and/or emails?
- Mandatory labelling – should users be required to apply a label to documents and/or emails?
- Provide justification – should users be prompted to provide a justification when changing a label?
Again, a good way to become familiar with these options is to start with a small set of test labels and explore the functionality of the different publishing options before a wider deployment.
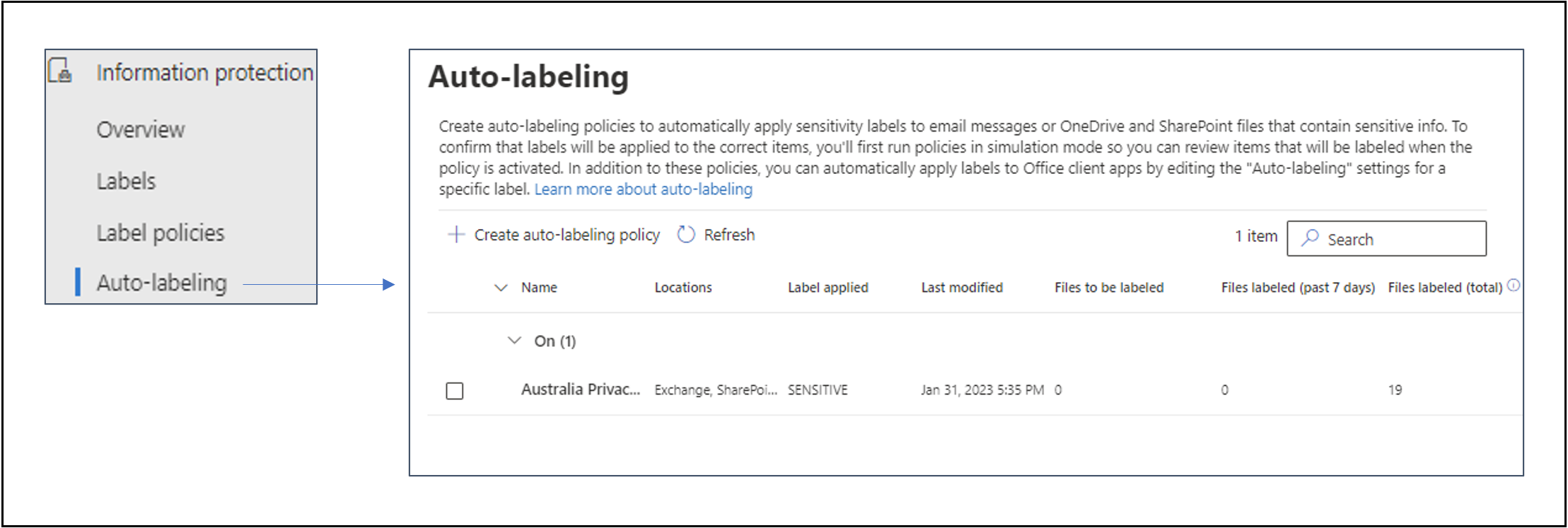
An alternative approach to publishing labels through a label policy is to apply auto-labelling. This will be the subject of a future post. When properly configured, Auto-labelling can be a powerful and flexible way to protect content without relying on users knowing when to use each of your classifications.
Like what you see?
Although Purview can appear complex, it offers an ever-growing range of capabilities to help protect you information in M365. Make sure you have suitable permissions assigned and then get started on your Purview journey.
If you would like to learn more then get in touch and let’s keep the conversation going.
Contact usAbout the author
Malcolm Bryce-Borthwick is a Senior Information Management Consultant at Engage Squared, with over 30 years of global experience in delivering effective information management solutions. He has extensive knowledge addressing information and records management challenges that make the best use of the continuously evolving M365 ecosystem, especially the ever-growing tools available in the Microsoft Purview compliance portal.
Malcolm is based in rural Tasmania, where he shares a patch of forest with a mob of friendly wallabies and several squadrons of raucous parrots.
This blog is part of our ‘modernise and secure teamwork with M365’ campaign. Follow us on LinkedIn as we share our insights across a series of blogs, client success stories, and events, as we explore how M365 can help solve today’s unique set of challenges.


